I have received some requests for more advanced posts regarding Log Insight so here is one for those requesting! I recently was asked how to query in Log Insight for when some subset of characters did not exist within a keyword. The specific question was in regards to Active Directory events. Let me walk you through an example and how to solve the problem.
To start, it is important to understand that Active Directory has three different types of Account Names in log messages:
- Username = <name>
- Computer = <name>$
- System = <name>SYSTEM
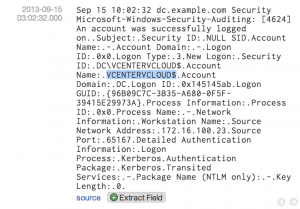
An example of an Active Directory event is as follows:
Sep 15 10:02:32 dc.example.com Security Microsoft-Windows-Security-Auditing: [4624] An account was successfully logged on..Subject:.Security ID:.NULL SID.Account Name:.-.Account Domain:.-.Logon ID:.0x0.Logon Type:.3.New Logon:.Security ID:.DC\VCENTERVCLOUD$.Account Name:.VCENTERVCLOUD$.Account Domain:.DC.Logon ID:.0x145145ab.Logon GUID:.{96B09C7C-3B35-A680-0F5F-39415E29973A}.Process Information:.Process ID:.0x0.Process Name:.-.Network Information:.Workstation Name:.Source Network Address:.172.16.100.23.Source Port:.65167.Detailed Authentication Information:.Logon Process:.Kerberos.Authentication Package:.Kerberos.Transited Services:.-.Package Name (NTLM only):.-.Key Length:.0.
The specific question was how to extract/query for account names that were usernames only. Given the question and thinking of how the query would be used, my recommendation was to extract the account name as a field and then check to see if it exists using a constraint. The issue was how to extract the field such that it would only extract the account name when it was a username.
To do this, select the account name (note: there are two and you want the second) and then select the Extract Field option. In the example above, this means highlighting VCENTERVCLOUD$ (a computer account name).
Upon selecting the Extract Field option, you will notice that the pattern selected does not work as expected. This is because the context selected exists twice within the event (I have filed a bug about this).
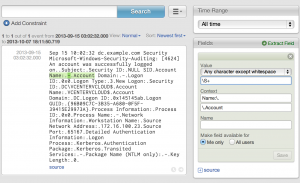
As such, the regular expression for the extracted field needs to be modified. Given the requirements, the Value regular expression is the hardest to figure out so I will say it until last. For the Context you want to be sure to include as many keywords as possible and also include a pattern that is guaranteed to match the account name as expected.
For the pre-context, I would recommend the following:
.*\.Account Name\:\..*\.Account Name\:\.
IMPORTANT: The duplication of the pattern is intentional because this event contains two account names. Without repeating the pattern then non-actual username names such as hyphen would be extracted if computer or system account names were found.
For the post-context, I would recommend the following:
\.Account Domain\:\.
IMPORTANT: The \:\. after Account Domain is critical because Account Domain or some variation of it is a valid account name.
As for the Value, all we know is that the username must be at least one character and can contain any characters. As such, the regular expression would look like the following:
.+
The problem with this value is that it includes any type of account name. To address this, you need to construct a does not contain regular expression. The does not contain regular expression for both computer and system account name types would look like the following:
((?!System|\$))
Next, you need to combine the two regular expressions in the Value field like this:
(.(?!System|\$))+
Finally, you want to be sure that the does not contain regular expression only applies to the end of the account name as contained anywhere else in the account name could be a valid username. To do this, the post-context of the field needs to be appended to the does not contain regular expression as follows:
(.(?!(System|\$)\.Account Domain\:\.))+
The end result would look like the following:
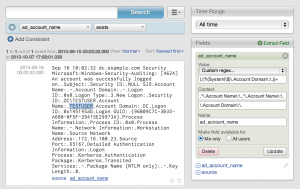
With the field created, you can now use a constraint for when the field exists to display account names that are only usernames.
© 2013 – 2021, Steve Flanders. All rights reserved.
